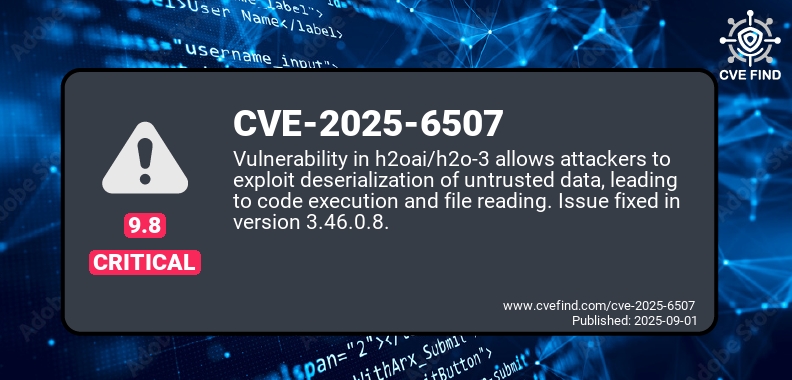
Code execution in h20ai/h2o-3
Published: Sep 01, 2025
A vulnerability in the h2oai/h2o-3 repository allows attackers to exploit deserialization of untrusted data, potentially leading to arbitrary code execution and reading of system files.
Summary
This issue affects the latest master branch version 3.47.0.99999. The vulnerability arises from the ability to bypass regular expression filters intended to prevent malicious parameter injection in JDBC connections. Attackers can manipulate spaces between parameters to evade detection, allowing for unauthorized file access and code execution. The vulnerability is addressed in version 3.46.0.8.
- Products: It affects Cisco Adaptive Security Appliance (ASA) Software and Cisco Firepower Threat Defense (FTD) Software.
- Problem Type: It is a vulnerability in the Site-to-Site IPsec VPN component of the software.
Exploitation
- Right, so we understand that the exploitation occurs in the weaknesses of regular expression pattern matching.
- Space Manipulation Technique
- The primary method identified involves manipulating spaces between parameters to evade detection by security filters.
- This technique specifically targets regular expression filters that are designed to prevent malicious parameter injection in JDBC connections.
- JDBC: JDBC (Java Database Connectivity) connections allow Java applications to interact with databases by providing a standard API for querying and updating data. They are established using a connection URL, which specifies the database type, server address, and other connection properties
- Filter Evasion Mechanism
- This approach allows malicious actors to:
-> Bypass parameter validation that relies on specific pattern matching.
-> Inject malicious parameters into JDBC connections undetected.
-> Exploit deserialization processes of untrusted data.
(An attacker sends a malicious, custom-built data packet to a system. The system blindly trusts this packet and, while processing it, is tricked into executing the attacker’s code instead of just reading data.) This vulnerability (CVE-2025-6507) carries a critical CVSS score of 9.8, highlighting the severe impact of successful filter bypass techniques
- This approach allows malicious actors to:
Mitigation
Organizations using h2oai/h2o-3 should immediately upgrade to version 3.46.0.8 to mitigate this high-severity security risk.