Redis
Redis
- Redis (Remote Dictionary Server) is an open-source, in-memory data structure store.
- Because it stores the data in RAM memory, it is very fast!
- Common Uses:
- Caching,
- message brokering,
- real-time analytics,
- session storage,
- leaderboards.
- Default Port: 6379 (TCP), also note that this port is not included in Nmap’s default top 1000 port scan.
Connecting to Redis
The following is a HackTheBox Lab:
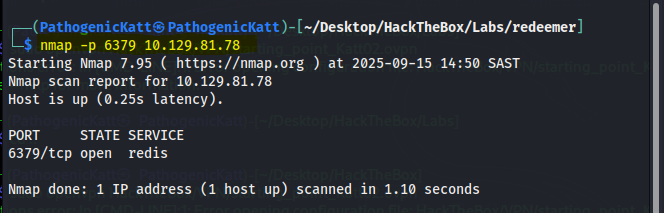
- Enumeration & Discovery
- As we know that, the default port of redis is 6379.
-p: specifies the port.- But notice the difference with the below enumeration:
sC: Default Script (checks vulnerabilities)sV: service version
- We are in!
-h: specifies the host- Now we have throw in, the command used within redis.
- Hence, our first command
info:
- Note i have highlighted, only the crucial info.
- For instance, we can look for exploits avalaible for that version:
- We see that we get nothing, but for older version; i’m sure we can get some exploits.
- But here is more, regarding the server:
- Now, our next command is
keys *, it displays the available keys: - From there we see our flag!
- And using
get flag, we get our flag.
Here are a couple more commands used in redis-cli
| Command | Description |
|---|---|
SELECT index |
Switches to a different database. Redis supports multiple databases (0-15 by default). |
TYPE key |
Returns the data type of a key (string, list, set, hash, etc.) |
CONFIG GET * |
Dangerous. Attempts to get all configuration parameters. |
Why Redis is a Target
- Exposed to the Network:
- By default, Redis binds to
127.0.0.1(localhost only) - If misconfigured to bind to
0.0.0.0, it becomes accessible from any network.
- By default, Redis binds to
- Arbitrary File Write:
- A Threat-Actor can manipulate Redis to write a file to any location the Redis server process has write permissions to.
.PNG)
.PNG)
.PNG)
.PNG)
.PNG)
.PNG)
.PNG)