Symmetric & Asymmetric Encryption
Symmetric & Asymmetric Encryption
Symmetric Encryption (Private-Key Cryptography)
- Also known as an conventional encryption and a single-key encryption.
- Is a form of cryptosystem in which encryption and decryption are performed using the same key or also as private-key encryption.
- Sender and receiver must have obtained copies of the secret key in a secure fashion and must keep the key secure, hence this justifies the name private key encryption.
- With the use of symmetric encryption, the principal security problem is maintaining the secrecy of the key.
- Some Terms:
- Plain-Text -> Original Message
- Cipher-Text -> Coded message
- The process of converting the plain-text to cipher-text -> Encryption/Enciphering.
- Restoring the plain-text from the cipher-text -> Decrption/Deciphering.
How does Symmetric Encryption Work?
- Key Generation
- So the first step is to generate the the private-key, this is generated through two methods; that is the Password-based key Derivation(PBKD) and hardware random number generators
- Encryption
- The plain-text is transformed to cipher-text through encryption-algorithm.
- Transfer of Cipher Text
- Here the coded-message, is transfered through the internet, and even if it is intercepted, the message will be un-readable.
- Decryption
- In the final step, the recipient uses the same secret key and a reverse encryption algorithm to convert the cipher text back into the original message (plain text).
Types of Symmetric Encryption Algorithms
-
| Algorithm | Key Size | Notes |
|---|---|---|
| AES(Advanced Encryption Standard) | 128-bits, 192-bits and 256-bits | Most widely used in CTF: ECB and CBC |
| DES(Data Encryption Standard) | 56-bits | Broken, and still appears in legacy challenges |
| Triple DES(3DES) | 168-bits | DES applied 3 times, but still slow and less efficient |
| Blowfish | variable(34-448 bits) | Older but still seen in some ctf |
| Twofish | 128-bit block size. Key sizes up to 256-bits | |
| RC4 | variable | stream cipher, often broken in ctf challenges |
Modes of Operation
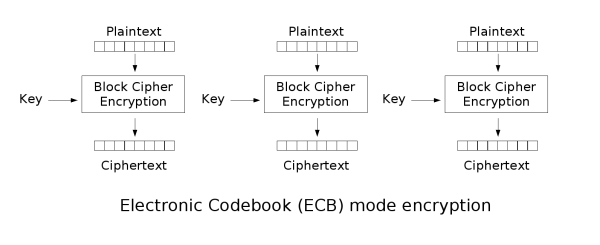
- ECB(Electronic Codebook) -> Insecure, reveals patterns (identical plaintext -> identical ciphertext), identical plaintext blocks produce identical ciphertext blocks, making it easier for attackers to infer information..
echo "katleho" | openssl enc -aes-128-ecb -nosalt -k passwd 2>/null/dev"katleho"is our input-k: stands for key; hence our key is passwd2>/null/devsilences the errors.
- CBC(Cipher Block Chaining) -> Uses an IV(Initialization Vector), vulnerable to padding oracle attacks.
from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad key = b'16_or_32_byte_key...' # Must be 16, 24, or 32 bytes data = b"secret message" # Encrypt cipher = AES.new(key, AES.MODE_CBC) ct = cipher.encrypt(pad(data, AES.block_size)) iv = cipher.iv # Needed for decryption # Decrypt cipher = AES.new(key, AES.MODE_CBC, iv) pt = unpad(cipher.decrypt(ct), AES.block_size) print(pt) # b'secret message' - CTR(Counter Mode) -> Turns block cipher into stream cipher, no padding needed.
- GCM(Galois/Counter Mode) -> Secure, provides authentication.
Asymmetric Encryption (Public-Key Cryptography)
- Uses different keys, public key for encryption and private-key to decryption.
Types of Symmetric Encryption Algorithms
| Algorithm | Based On | CTF relevance |
|---|---|---|
| RSA(Rivest–Shamir–Adleman) | Integer Factorization | Most Common in CTF(small primes and faulty keys) |
| Diffie-Hellman(DH) | Discrete Algorithm | Key Exchange Challenges |
| Elleptic Curve Cryptography(ECC) | Elleptic Curves | Less common but growing |
How RSA Works
- Choose two large prime numbers p and q
- Compute modulus(n) which is (p * q)
- Compute phi(n) = (p-1)*(q-1)
- Choose e (public exponent, often 65537)
- Compute d(private exponent) = (e^-1) * mod(phi(n))
- Encrypt:
ciphertext = plaintext^e * mod(n) - Decrypt:
plaintext = ciphertext^d * mod(n)
Key Differences
| Feature | Symmetric | Asymmetric |
|---|---|---|
| Key Used | Same Key for encryption/decryption | Public + Private Key pair |
| Speed | Fast(good for large data) | slow (used for key exchange) |
| Key Exchange | Must be shared secured | No need to share private key |
| CTF Usage | ECB/CBC attacks, brute-force | RSA factorization |