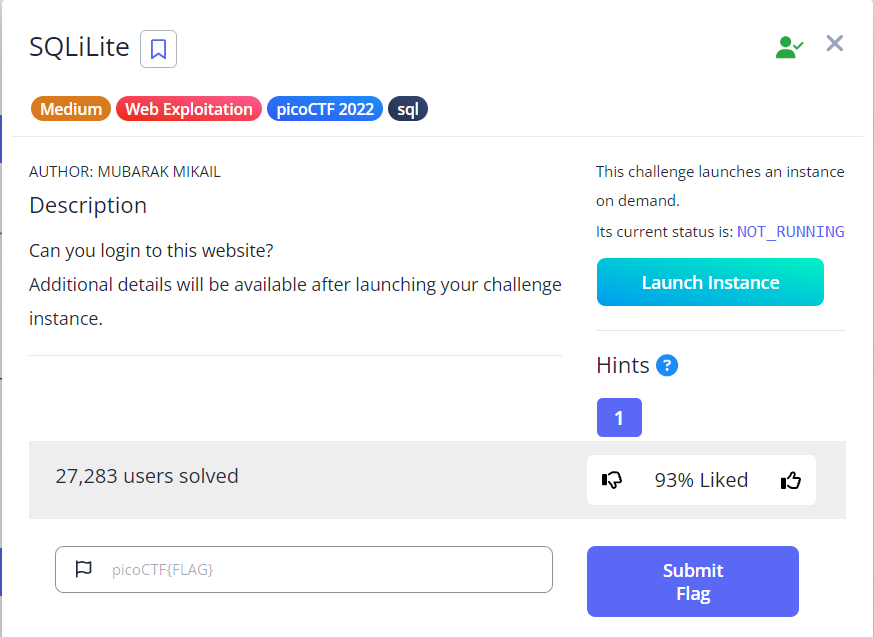
PicoCTF Challenge: SQLiLite
Challenge Overview:
- The following was the description for the challenge:
Deep Dive
- Can we login?
- First we test, the behavior of the website:
- clicking the login button:
- hence, we can see that, the web uses some SQL. From here; just like any other hacker. This is what i did:
- Common payload:
username: admin' -- password: gibberish - The password is ignored by the use of the sql comments “
--”. So everthing after the comment will be ignored:
- Common payload:
- Hence, the output:
The flag
- View the source code:
Ctrl+u- On Windows.
.PNG)
.PNG)
.PNG)
.PNG)
.PNG)