TryHackMe Challenge: Smol
Executive Summary
The objective of this report is to document the successful exploitation path for the TryHackMe challenge “Smol.” The target is a WordPress-based virtual machine that includes a publicly known vulnerable plugin and a backdoored plugin. This exercise demonstrates the importance of secure plugin management, software patching, and source-code review in web application security.
Objective
- Obtain the user flag from the target machine.
- Obtain the root flag from the target machine.
Scope
- Target: WordPress web application hosted on the Smol VM.
- Focus: reconnaissance, application enumeration, vulnerability identification, exploitation, and privilege escalation.
Challenge Description
The Smol machine is centered on a WordPress website. It is designed to teach reconnaissance and exploitation of WordPress plugin vulnerabilities, including backdoored third-party components. The challenge highlights how outdated or malicious plugins can expose a web application to compromise.
Methodology
- Reconnaissance: Identify available services, web application endpoints, and WordPress components.
- Enumeration: Enumerate plugins, themes, users, and potential misconfigurations.
- Vulnerability analysis: Assess identified plugins for known vulnerabilities and malicious code.
- Exploitation: Execute the exploit chain to obtain initial access and escalate privileges.
- Validation: Confirm user and root flag acquisition.
Key Findings
- The target is a WordPress site with a vulnerable plugin.
- The challenge includes a backdoored plugin, demonstrating the risk of installing untrusted third-party code.
- Successful exploitation leads to user-level access and subsequent privilege escalation to root.
Technical Reconstruction
Reconnaissance
- Describe the tools and techniques used to enumerate the target.
- Record discovered web application paths, WordPress version, and plugin list.
- Using nmap, a network mapping that allows us to see what ports are open and what services are running on those ports:
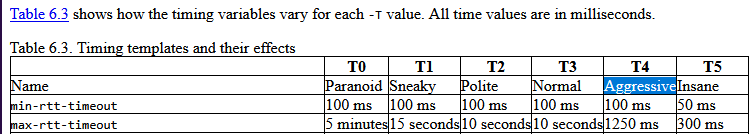
nmap -p- -A -T4 <ip-address> -p-: “scans for all 65,535 ports”.-A: “scans aggressively, it includes-sC(script scanning),-sV(Version of the service running),-O(type of operating system)”.-T4:
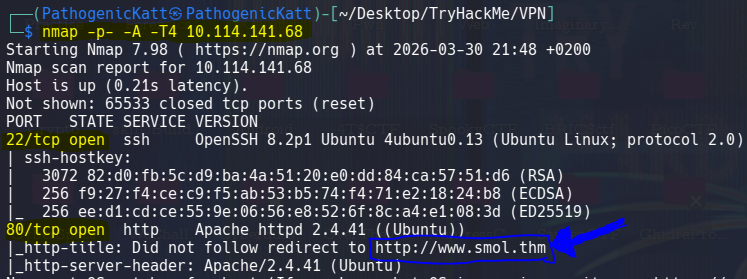
- results:
- From above results we see that we have two open ports,
port 22andport 80. - The blue highlighted section gives us a hint that we have to register the Ip-Address under /etc/hosts as smol.thm, so we can be able to work with the able properly.
sudo sh -c 'echo "<ip-address> smol.thm" >> /etc/hosts' - becareful
>>appends, while>will overwrite the file.
- From above results we see that we have two open ports,
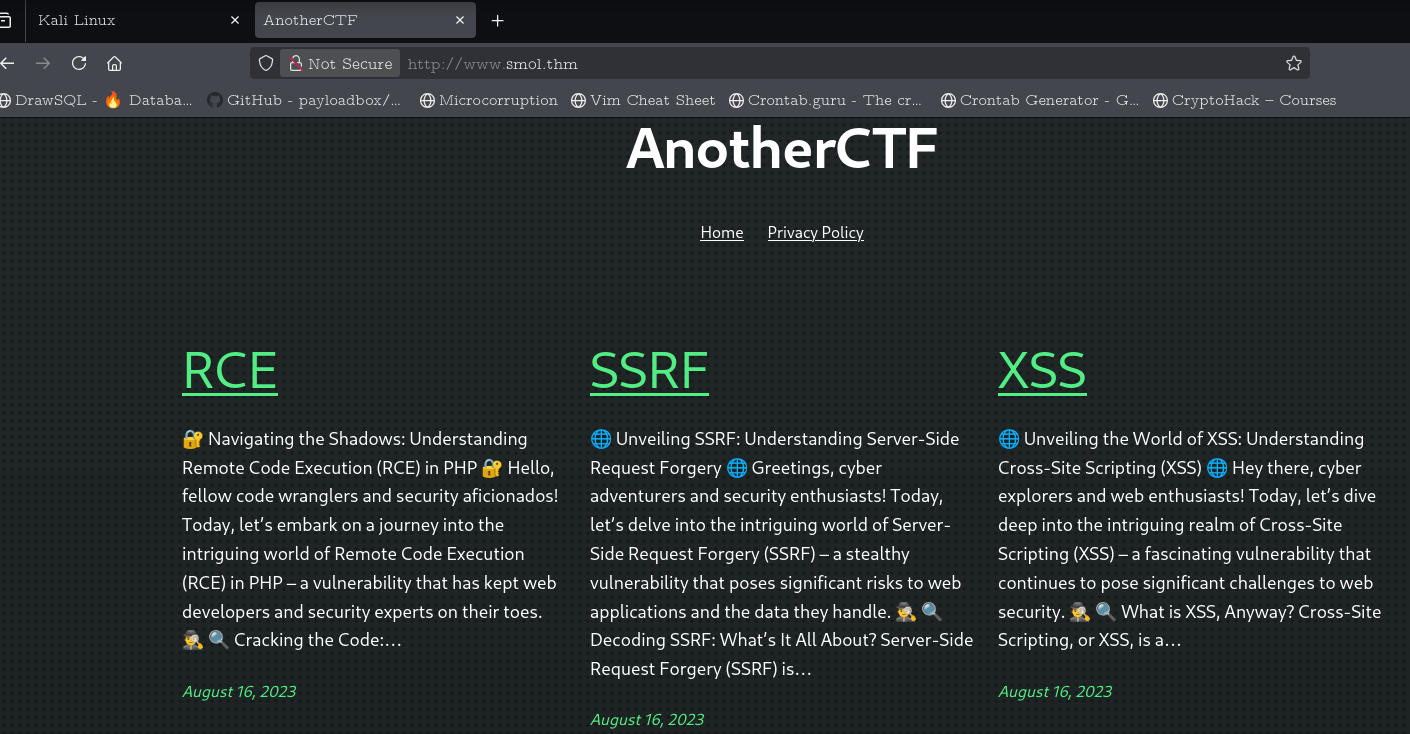
- Hence the landing page:
- Since the landing page is a blog posts about (Cross site scripting) XXS, (Remote Execution) RCE, and (Server Side Request Forgery) SSRF, it made sense to think or to have an idea that these are the techniques that the website is vulnerable to.